Handala hackers breach Hebrew Academy website, sparking concern across the education sector after the hacktivist group claimed responsibility for infiltrating the school’s online platform. The cyber incident disrupted access to parts of the website and prompted immediate action from administrators and technology teams working to secure the system and restore normal operations.
Educational institutions across the United States increasingly depend on websites and digital platforms to communicate with students, parents, and staff. When a school’s online system experiences unauthorized access, administrators must respond quickly to protect sensitive data and maintain trust within the community. In this case, the breach drew attention not only from the local school community but also from cybersecurity observers tracking hacktivist activity targeting educational institutions.
The event highlights how school websites, despite appearing simple on the surface, remain part of larger digital ecosystems that require strong cybersecurity protections.
Overview of the Hebrew Academy School Network
Hebrew Academy schools operate across several regions and typically provide private education focused on both general academic studies and Jewish cultural or religious education. These institutions often maintain online platforms that support communication with families, manage school announcements, and provide access to student resources.
Modern school websites usually serve multiple purposes.
Typical website functions include:
- Publishing academic calendars and event schedules
- Providing contact information for faculty and administration
- Hosting student resources and homework portals
- Displaying admissions information for prospective families
- Sharing community announcements and school updates
Because of these roles, the website often acts as the primary communication hub between the school and the broader community.
When attackers disrupt such a platform, even temporarily, it can interrupt access to information that families rely on daily.
How the Cyberattack Became Public
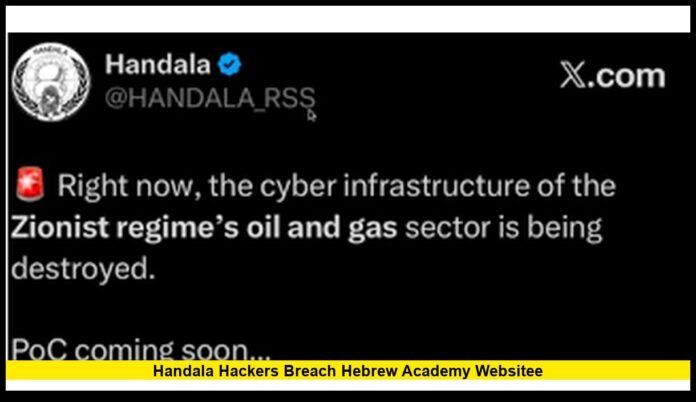
The cyber incident gained public attention after the hacking group known as Handala claimed responsibility for breaching the Hebrew Academy website.
Hacktivist groups often announce cyber operations through online channels used to promote political messaging. These announcements frequently appear shortly after the attack occurs, sometimes accompanied by screenshots or statements intended to demonstrate access to the targeted system.
Once the breach became visible, the school’s administrators and technical personnel began investigating the intrusion.
Initial actions typically include:
- Reviewing server activity logs
- Identifying how attackers accessed the system
- Securing administrative accounts
- Temporarily limiting access to parts of the website
These steps help organizations prevent attackers from maintaining access while security teams evaluate the full scope of the incident.
Who Are the Handala Hackers
The group associated with the attack has appeared in multiple cyber incidents involving organizations connected to Israeli or Jewish institutions.
Handala is widely described by cybersecurity analysts as a hacktivist collective. Hacktivist groups often conduct cyber operations as a form of digital protest tied to political or ideological viewpoints.
Their activities typically focus on public visibility rather than financial gain.
Common tactics used by hacktivist groups include:
- Website defacement attacks
- Claims of data theft or leaks
- Distributed denial-of-service disruptions
- Posting political messages on compromised platforms
These attacks aim to attract attention and amplify political messages through online visibility.
While the technical damage may vary from case to case, such incidents often create reputational and security concerns for targeted organizations.
What Happens During a Website Breach
A website breach occurs when attackers gain unauthorized access to a website’s underlying systems.
Hackers often exploit vulnerabilities in software or weak authentication controls to enter the system.
Once attackers gain access, several outcomes are possible.
Common actions during website intrusions include:
- Modifying website content
- Uploading unauthorized files or scripts
- Accessing stored data
- Redirecting visitors to external pages
The most visible form of website attack is defacement, where attackers replace legitimate pages with their own messages or images.
Even if attackers do not access sensitive data, defacement can disrupt communication and damage public trust.
Why Educational Institutions Become Targets
Educational organizations increasingly rely on digital infrastructure for daily operations.
This digital transformation has created new opportunities for cyber attackers.
Schools and universities may become targets for several reasons.
Public Visibility
School websites are often accessible to anyone on the internet, making them visible targets for cyber campaigns.
Limited Cybersecurity Resources
Some educational institutions operate with smaller IT teams compared with large corporations.
Community Impact
Attacking a school website can generate attention because families, students, and community members depend on the platform.
Political Messaging
Hacktivist groups sometimes select targets based on ideological motivations.
These factors make educational institutions part of the broader cybersecurity landscape.
Immediate Security Response
When administrators discovered the breach, technical teams focused on stabilizing the website and preventing additional unauthorized access.
Organizations typically follow a structured incident response process.
Initial response actions often include:
- Temporarily disabling affected website components
- Resetting administrator passwords
- Updating software used by the website
- Scanning servers for malicious code
Security specialists may also analyze whether attackers accessed databases connected to the website.
If sensitive data appears at risk, organizations may conduct additional investigations and strengthen access controls.
Website Infrastructure and Vulnerabilities
School websites often run on widely used content management systems that allow administrators to update pages without advanced programming knowledge.
These systems offer convenience but require consistent security maintenance.
Common vulnerabilities in website infrastructure include:
- Outdated software versions
- Weak administrator passwords
- Misconfigured server settings
- Unpatched security flaws in plugins or extensions
Attackers frequently scan the internet searching for websites with these weaknesses.
Regular software updates and security monitoring help reduce the risk of exploitation.
The Importance of Protecting School Data
Educational institutions maintain various forms of data within their digital systems.
Although the primary impact of the breach involved website functionality, schools must ensure that internal databases remain secure.
Typical data managed by educational systems includes:
- Student enrollment records
- Parent contact information
- Academic schedules and materials
- Faculty contact directories
Protecting this information remains a top priority during cybersecurity investigations.
Schools often work with security specialists to confirm that attackers did not access sensitive records.
Cybersecurity Measures for School Websites
Following incidents like this, educational institutions often strengthen their digital defenses.
Several security practices help protect school websites.
Recommended cybersecurity measures include:
- Implementing multi-factor authentication for administrators
- Using web application firewalls to filter malicious traffic
- Regularly updating website software and plugins
- Monitoring website traffic for unusual activity
Schools may also schedule periodic security assessments to identify vulnerabilities before attackers exploit them.
These assessments help maintain stronger digital protection.
The Growing Challenge of Hacktivism
Hacktivism has emerged as a noticeable trend within the global cybersecurity landscape.
Groups driven by political or ideological motivations increasingly target organizations they believe represent opposing viewpoints.
Targets can include:
- Government agencies
- Corporations linked to geopolitical issues
- Educational institutions
- Nonprofit organizations
Hacktivist campaigns often focus on high-visibility actions such as website defacement or public data leak claims.
Even when technical damage remains limited, the visibility of these incidents can draw widespread attention.
Community Reaction to the Incident
When news spread that handala hackers breach hebrew academy website, members of the school community expressed concern about the security of online systems.
Parents rely on school websites for important updates regarding schedules, events, and announcements.
Temporary disruptions can interrupt communication and create uncertainty.
School administrators typically address these concerns by communicating updates and outlining steps taken to strengthen cybersecurity protections.
Transparent communication helps maintain trust between schools and families.
Lessons for Educational Institutions
The cyber incident demonstrates several lessons for schools operating online platforms.
Educational institutions must treat website security as an essential part of their technology strategy.
Key lessons include:
- Maintain updated website software and security patches
- Limit administrative access to authorized personnel
- Monitor website activity continuously
- Prepare incident response plans for cyber events
These steps help reduce the likelihood of future breaches.
Cybersecurity Awareness in Schools
Cybersecurity education has become increasingly important for school staff and administrators.
Even simple actions can reduce the risk of cyber incidents.
Training programs often focus on:
- Recognizing phishing emails
- Creating strong passwords
- Reporting suspicious online activity
- Following secure login procedures
Staff members who manage digital platforms benefit from additional training on website security practices.
Education remains one of the strongest defenses against cyber threats.
Looking Ahead for School Cybersecurity
Educational institutions continue expanding digital services for students and families.
Online learning platforms, communication systems, and school websites all form part of modern education infrastructure.
As these systems grow more complex, cybersecurity protection becomes even more important.
Schools increasingly invest in monitoring tools, security training, and technology upgrades to protect their online platforms.
Strong cybersecurity measures help ensure that school communities can rely on digital services safely and consistently.
What steps do you think schools should take to strengthen cybersecurity and protect their online platforms? Share your thoughts and stay informed about the latest developments in digital security for education.