Cyber attacks Stryker experienced in March 2026 disrupted internal networks across one of America’s largest medical device manufacturers, forcing widespread system shutdowns and raising alarms across the healthcare technology sector. The Michigan-based company confirmed that a significant cybersecurity incident affected corporate systems, internal communication platforms, and employee devices used across multiple regions.
The disruption quickly drew attention from cybersecurity experts and healthcare organizations because of Stryker’s major role in supplying technology used in hospitals worldwide. Investigators are still working to determine the full scope of the attack and how the intrusion occurred.
Major Cybersecurity Incident Hits Stryker
Stryker Corporation is a leading U.S. medical technology company headquartered in Portage, Michigan. The company develops surgical equipment, orthopedic implants, hospital beds, and advanced medical devices used by healthcare providers around the world.
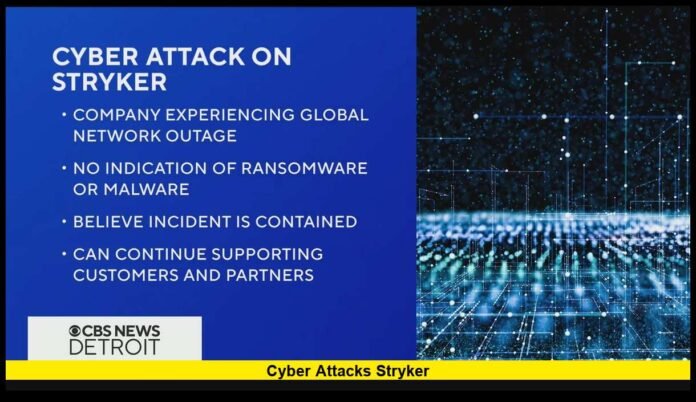
On March 11, 2026, company officials confirmed that a cyberattack disrupted global network operations. Internal systems used by employees became inaccessible as cybersecurity teams responded to the incident.
The disruption forced the company to isolate parts of its network while investigators assessed the situation and worked to restore normal operations.
Key confirmed developments include:
- Corporate networks affected across multiple regions
- Thousands of employee devices disconnected from systems
- Internal communication tools temporarily unavailable
- Emergency cybersecurity containment measures activated
The company acted quickly to protect its systems by limiting network access while experts analyzed the intrusion.
Hacking Group Claims Responsibility
Shortly after the attack became public, a hacking group known as Handala claimed responsibility online. Cybersecurity researchers have previously associated the group with operations linked to Iran.
Online statements attributed to the group suggested the cyberattack targeted the company in response to geopolitical tensions. The hackers also claimed they obtained internal company data during the operation.
Authorities and cybersecurity investigators have not verified all of the claims made by the group. However, analysts say the group has previously been involved in disruptive cyber campaigns targeting international organizations.
Signs of a Possible Wiper Malware Attack
Initial analysis from cybersecurity specialists suggests the attack may have involved destructive malware known as a wiper.
Unlike ransomware, which locks files and demands payment, wiper malware permanently deletes or damages data stored on systems. The goal is usually disruption rather than financial gain.
Typical features of wiper malware attacks include:
- Overwriting important system files
- Permanently deleting stored data
- Preventing computers from restarting properly
- Creating large-scale network outages
Experts believe the attack may have disabled thousands of corporate devices connected to the company’s internal infrastructure.
If confirmed, the incident would represent one of the most disruptive cyberattacks against a global healthcare technology company in recent years.
No Ransom Demand Reported
Despite the severity of the disruption, investigators have not reported any ransom demand tied to the cyberattack.
Most large corporate cyber incidents today involve ransomware groups attempting to extort payment from companies. In this case, there has been no evidence suggesting that attackers attempted to negotiate or demand money.
Cybersecurity specialists believe the attack may have focused primarily on disrupting operations rather than generating financial profit.
Impact on Employees and Global Operations
The cyberattack quickly affected Stryker’s global workforce. Employees across several regions reported losing access to internal systems, communication platforms, and corporate tools.
As part of containment efforts, internal IT teams shut down sections of the company’s network to stop the attack from spreading further.
Operational disruptions included:
- Thousands of employee laptops and devices taken offline
- Corporate messaging and communication systems disrupted
- Temporary interruption of internal business tools
- Cybersecurity teams working around the clock on recovery
Facilities in Europe also experienced system outages when networks were disconnected as a safety precaution.
Despite these challenges, the company activated internal contingency plans to maintain support for hospitals and healthcare partners.
Why the Healthcare Sector Is Concerned
The attack attracted significant attention because Stryker plays a crucial role in the global healthcare supply chain.
The company produces medical technologies used daily in hospitals and surgical centers, including:
- Orthopedic implants and joint replacement devices
- Surgical imaging and navigation technology
- Endoscopy equipment
- Emergency medical devices
- Hospital beds and patient support systems
Healthcare organizations rely on these products to support patient care and surgical procedures.
Cybersecurity experts warn that attacks targeting manufacturers could potentially create broader disruptions within healthcare systems if production or distribution is affected.
Growing Threats to Healthcare Technology Companies
Cybersecurity specialists have increasingly warned that healthcare organizations and medical technology suppliers face growing risks from cyberattacks.
These companies manage large networks, valuable intellectual property, and sensitive operational data. This combination makes them attractive targets for sophisticated hackers.
Recent cyber incidents across the healthcare industry show a rise in attacks aimed at disrupting services or accessing confidential information.
Experts believe geopolitical tensions may also influence cyber activity targeting major corporations involved in critical infrastructure.
Investor Reaction and Market Impact
News of the cyberattack also triggered a reaction in financial markets. Investors closely monitor cybersecurity incidents involving large technology companies because operational disruptions can affect revenue and business continuity.
Following reports of the attack, Stryker’s stock price experienced a decline as investors evaluated the potential impact of the disruption.
Market analysts continue watching the situation as the company works to restore systems and complete its cybersecurity investigation.
Investigation and Recovery Efforts Continue
Cybersecurity teams inside the company, along with external investigators, are continuing to analyze how the attack occurred.
The investigation is focused on several key areas:
- Identifying the entry point used by attackers
- Determining whether data was accessed or removed
- Measuring the number of affected systems
- Restoring network operations safely
System recovery often takes time after large cyber incidents because organizations must verify that networks are secure before reconnecting them.
Digital forensic specialists also analyze logs and system data to ensure attackers no longer have hidden access to company infrastructure.
What the Cyberattack Means for Corporate Security
The cyber attacks Stryker experienced highlight how modern cyber threats are evolving beyond simple financial extortion.
Some attacks now focus on disrupting operations or sending political messages rather than seeking payment. Companies involved in healthcare, infrastructure, and technology are especially vulnerable because their services are essential to everyday life.
Security experts say organizations must strengthen protection through multiple strategies:
- Continuous network monitoring
- Advanced threat detection tools
- Stronger access control systems
- Comprehensive employee cybersecurity training
These defensive measures help reduce the risk of future incidents and allow organizations to respond more quickly if an attack occurs.
The cyber attacks Stryker faced demonstrate how vulnerable even major healthcare technology companies can be in today’s digital environment. What do you think companies should do to strengthen cybersecurity in critical industries?