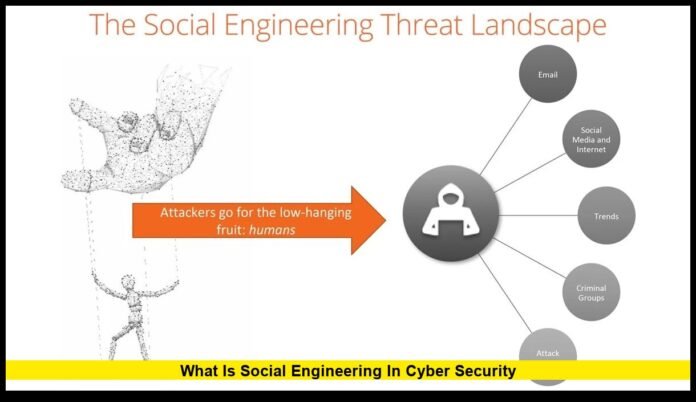
Social engineering in cyber security has become one of the most urgent challenges facing the United States in 2025. Attacks that rely on manipulating people rather than breaking into computer systems now dominate many of the nation’s most disruptive breaches. As hackers grow more skilled at mimicking trusted voices, crafting believable digital messages, and exploiting moments of confusion or stress, Americans face a threat that evolves faster than most defenses can adapt.
Unlike malware or technical intrusions, these schemes target human nature itself. They exploit trust, urgency, fear, curiosity, and routine patterns that most people never think twice about. With the rise of artificial intelligence, more persuasive impersonation tools, and an increase in attacks on third-party platforms, social engineering has transformed into a national digital concern that continues to escalate.
A Clear Look at What Social Engineering Really Is
Social engineering is a technique used by attackers to gain sensitive information, account access, or system entry by manipulating people. It can occur over email, text messages, phone calls, video messages, chat platforms, or even in person. The tactics vary widely, but the goal is consistent: convince a person to perform an action that benefits the attacker.
Some criminals pretend to be bank representatives. Others impersonate coworkers, executives, government officials, customer-service staff, or technical support agents. These interactions feel authentic because attackers study the behavior, structure, and communication style of real organizations.
In many cases, an employee or individual unknowingly helps the attacker by sharing a verification code, clicking a harmful link, entering credentials into a fake website, or approving a login request they did not initiate. Once a single mistake occurs, the damage can spiral quickly.
Why These Attacks Have Become So Effective
1. AI Is Making Scams More Convincing
Attackers now generate realistic emails, phone messages, and scripts that closely match the communication patterns of established companies. AI tools create lifelike voices that mimic real people. Even seasoned professionals can struggle to distinguish a fraudulent request from a legitimate one.
2. Americans Are Overloaded With Alerts and Notifications
Daily life now involves nonstop messages from banks, delivery services, workplaces, retailers, and apps. Attackers exploit this overload. When a text claims there is a “fraud alert,” “account lock,” or “package exception,” many people react quickly without verifying the message.
3. Third-Party Systems Are Increasingly Targeted
Many U.S. organizations rely on outside platforms for customer support, onboarding, communication, data storage, or payment processing. Criminals are aware that these external systems may be less secure than the primary company. By manipulating someone at a vendor, attackers gain access to information that can be used to impersonate the victims more effectively.
4. Financial Institutions Face Constant Pressure
Banks and payment platforms frequently face account-takeover attempts. Attackers take advantage of busy customer-service lines, fatigued employees, and automated verification systems. When combined with personal information available online, it becomes easier for criminals to impersonate legitimate customers.
Common Methods Used in Today’s Social Engineering Attacks
Phishing
Fraudulent emails designed to trick people into entering passwords, downloading malware, or clicking harmful links. These emails often look identical to legitimate corporate messages, complete with company logos and accurate formatting.
Spear Phishing
Highly personalized attacks that target specific individuals. Criminals reference job roles, internal projects, or current company initiatives to appear trustworthy.
Vishing
Phone-based manipulation, sometimes conducted by AI-generated voices. Attackers may claim to be from IT, HR, a bank, or a government agency, pressing victims to act quickly.
Smishing
Text-message scams sent under the guise of delivery updates, financial alerts, reward programs, or security notifications.
Pretexting
A detailed scenario crafted to gain the victim’s confidence—for example, posing as a company technician investigating an urgent system issue or an HR representative conducting an internal audit.
Baiting
Luring victims with downloads, offers, rewards, or attachments that contain malicious content.
MFA Fatigue Attempts
Repeated login prompts are sent to the victim’s device. When overwhelmed or distracted, the person may approve a request they did not initiate, granting the attacker immediate access.
Recent U.S. Trends Driving the Surge
Attacks Using Realistic Corporate Language
Messages now mirror the exact tone and style that departments like finance, payroll, or human resources use. Criminals pull publicly visible information from company websites, job boards, and social profiles to build credibility.
Greater Focus on Customer-Service Employees
Support workers have access to valuable customer data. They often juggle high call volumes, making them prime targets for deception. A single manipulated employee can unintentionally provide information used to infiltrate a much larger system.
Credential Harvesting Through Fake Login Portals
Attackers create login pages identical to those of major banks, cloud platforms, and retail services. When victims enter their username and password, criminals capture the information instantly.
Higher Volume of Attacks During Busy Seasons
Scammers time their attempts around holidays, tax season, major shopping periods, and election cycles. These moments generate confusion and urgency, making people more vulnerable.
The Real-World Consequences for Americans
Social engineering attacks cause damage that goes far beyond stolen passwords or temporary inconvenience. The consequences can reshape a person’s financial stability, disrupt business operations, and expose sensitive personal information.
Financial Loss
Unauthorized transfers, fraudulent withdrawals, and account takeovers can drain accounts before banks detect unusual activity.
Identity Theft
Stolen Social Security numbers, dates of birth, and addresses may be used to open fraudulent credit lines, commit tax fraud, or apply for loans.
Corporate Breaches
Employees who unknowingly provide attackers with system access can trigger major incidents affecting thousands or even millions of customers.
Loss of Personal Data
Medical details, insurance records, travel itineraries, and private communications can be exposed and misused.
Long-Term Damage to Trust
Customers lose confidence in a company if they feel their information was mishandled or used to facilitate scams. Rebuilding trust can take years.
Notable U.S. Incidents Illustrating Today’s Threat Level
The United States has seen several verified incidents in 2025 in which attackers manipulated individuals to obtain data or system access. These incidents share common patterns: emotional manipulation, urgency, impersonation, and exploitation of third-party systems.
In one case, criminals targeted a support agent at a platform used by major enterprises. By pretending to be internal staff, they convinced the agent to release customer account information. Although critical financial data remained protected, the stolen contacts and case details were enough to fuel follow-up scams directed at large corporations.
Another case involved a well-known delivery service where an employee interacted with what appeared to be a routine internal inquiry. The attacker gained entry to internal tools and accessed sensitive customer profiles. While payment information stayed secure, the exposed personal details increased the risk of impersonation attacks on millions of users.
Financial platforms also suffered breaches after attackers manipulated employees at vendor-operated customer-service centers. In these cases, criminals gathered personal data that allowed them to impersonate customers more convincingly during later attempts to take over accounts.
These incidents demonstrate that modern attackers rarely rely on brute-force hacking. Instead, they leverage access to information, human inconsistency, and psychological cues.
How Organizations Across the U.S. Are Strengthening Defenses
Frequent, Realistic Training
Companies now simulate actual attacks to teach employees how to recognize suspicious messages and unexpected requests. These simulations reflect real threats rather than generic examples.
Tighter Access Controls
Employees receive only the permissions necessary for their role. Limiting access reduces the impact if an account is compromised.
Improved Authentication Standards
Businesses use multi-factor authentication, security keys, and zero-trust models to verify identity before granting system access.
Regular Vendor Audits
Organizations evaluate the security practices of customer-support firms, data processors, and cloud-service providers to ensure they meet modern standards.
Rapid Response Protocols
Security teams rehearse procedures for containing compromised accounts, revoking access, and minimizing disruption to services.
How Individuals Can Stay Safer
Stay Skeptical of Unexpected Messages
Unusual requests to verify accounts, confirm personal information, or click urgent links should be checked directly through official channels.
Use Strong, Unique Passwords
Avoid repeating passwords across multiple websites. A single breach could otherwise expose several accounts.
Enable Multi-Factor Authentication
This adds a crucial layer of security, especially for financial and email accounts.
Avoid Approving Unrequested Login Prompts
If a login request appears out of nowhere, deny it immediately and change your password.
Verify Before Sharing
If someone contacts you claiming to be from a company, call the organization directly using the official number from its website.
Check Accounts Frequently
Regular monitoring helps detect unusual activity early.
Keep Software Updated
Security patches help prevent malware or fraudulent tools from operating effectively.
Why Social Engineering Will Continue to Grow
This threat continues to expand because the methods work. Humans are inherently trusting, especially when they believe they are speaking to an authority figure, a coworker, or a familiar brand. Technology cannot change this basic element of human behavior. Attackers know this and continue to refine their strategies.
AI will make impersonation more realistic. More companies will outsource processes to third-party platforms, creating additional points of vulnerability. Criminal networks will continue targeting groups with high volumes of digital communication—workers, students, seniors, freelancers, and everyday online shoppers.
As long as people respond quickly to digital communications, social engineering will remain a powerful tool for attackers.
Final Thoughts
Social engineering in cyber security has become a central issue in America’s digital landscape. Attackers now rely on emotion, urgency, and psychological pressure rather than technical force. The threat is more personal, more targeted, and more sophisticated than ever. Protecting against it requires awareness, skepticism, and a clear understanding of how these schemes work. Staying alert today can prevent significant loss tomorrow.
If you’ve encountered suspicious messages or seen emerging scam trends, feel free to share your experience with other readers below.