Cybersecurity experts and organizations are increasingly concerned with what is social engineering in cyber security, as it remains one of the most effective methods attackers use to exploit individuals. Social engineering targets human psychology rather than technical systems, tricking people into sharing sensitive information, clicking malicious links, or performing actions that compromise security. Understanding social engineering, identifying its methods, and implementing preventive measures are essential to protect both personal and organizational data.
Key Points Summary
Social engineering in cyber security manipulates human behavior to gain unauthorized access to information or systems. Common techniques include phishing, spear phishing, pretexting, baiting, tailgating, vishing, and smishing. The consequences of attacks range from data breaches and financial loss to reputational damage. Prevention requires a combination of employee training, security policies, multi-factor authentication, email filters, and constant vigilance. Recognizing suspicious communications and verifying requests are critical components of defense.
Understanding Social Engineering in Cyber Security
Social engineering is an attack strategy that targets people rather than software vulnerabilities. Attackers often impersonate trusted figures, such as coworkers, IT staff, or service providers, to manipulate victims into revealing passwords, personal data, or financial information. Unlike malware-based attacks, social engineering relies on psychological manipulation, exploiting traits like trust, fear, urgency, and curiosity. Organizations must understand the tactics used and train employees to respond cautiously to unusual requests.
Common Types of Social Engineering Attacks
Social engineering encompasses various attack methods designed to exploit human behavior:
Phishing: Fraudulent emails or messages prompt recipients to provide sensitive information or click malicious links.
Spear Phishing: A personalized phishing attempt that targets specific individuals with information gathered about them.
Pretexting: Creating a false scenario or identity to obtain confidential information, such as posing as IT support requesting credentials.
Baiting: Leaving infected USB drives or devices in public areas to entice victims into using them, which installs malware.
Tailgating: Gaining physical access to restricted areas by following authorized personnel without proper authorization.
Vishing: Using phone calls to deceive individuals into sharing confidential information.
Smishing: Delivering fraudulent requests or malicious links via SMS messages.
Recognizing these attack types helps individuals and organizations implement effective defenses and respond appropriately to threats.
Why Social Engineering is Highly Effective
Social engineering succeeds because it targets human weaknesses that cannot be patched like software vulnerabilities. Factors making it effective include:
- Trust in colleagues, authority figures, or known contacts
- Fear of consequences or urgency to act quickly
- Curiosity about unexpected emails, messages, or links
- Desire to help or assist others
Even the most advanced technical security measures cannot prevent attacks if human behavior is exploited, emphasizing the need for awareness and training.
Recent Examples of Social Engineering Attacks
In 2025, social engineering has been behind several high-profile security breaches:
- Corporate phishing campaigns targeting financial institutions led to unauthorized fund transfers.
- Spear-phishing attacks compromised government email accounts and exposed sensitive data.
- Baiting at conferences caused malware infections in company laptops, disrupting operations.
These cases highlight that attackers often combine technical knowledge with psychological manipulation, making vigilance crucial.
Impact of Social Engineering on Organizations
The consequences of social engineering attacks can be severe and multi-faceted:
- Financial loss from fraudulent transactions or ransomware attacks
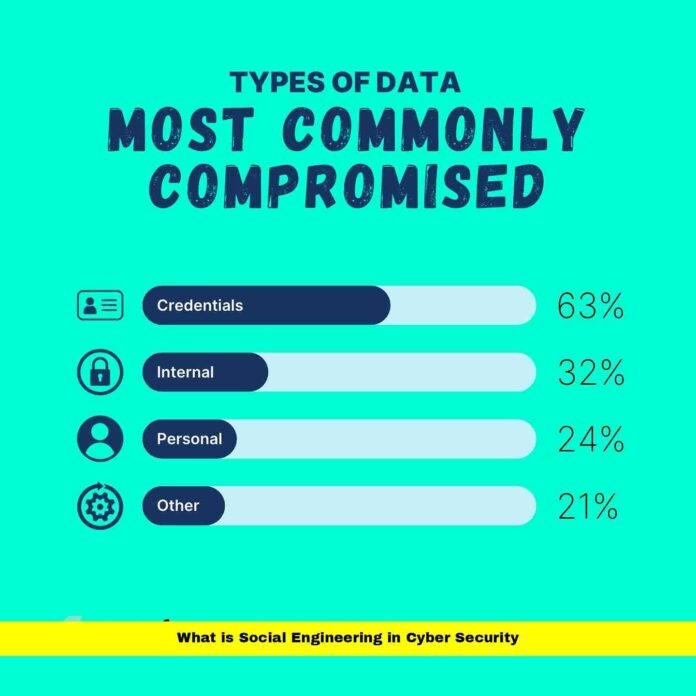
- Data breaches exposing client, employee, or corporate information
- Legal and regulatory penalties for failing to secure sensitive data
- Reputational damage and loss of customer trust
- Operational disruptions due to compromised systems or human error
Addressing social engineering threats requires a combination of proactive measures, employee education, and robust security protocols.
Preventing Social Engineering Attacks
Defending against social engineering requires both human awareness and technical safeguards:
- Employee Training: Regular workshops teach employees to recognize phishing emails, suspicious phone calls, and other manipulation attempts.
- Multi-Factor Authentication: Adds layers of protection even if login credentials are compromised.
- Email Filters and Security Tools: Detect malicious messages before they reach users.
- Verification Procedures: Require confirmation of unusual requests for sensitive data.
- Security Audits: Regular reviews identify potential vulnerabilities and improve defenses.
Combining these measures creates a multi-layered defense strategy that strengthens organizational resilience.
Role of Cybersecurity Policies
Clear policies help organizations mitigate social engineering risks:
- Define acceptable use of company devices and systems
- Mandate reporting of suspicious communications
- Enforce strong password management practices
- Establish protocols for granting access to sensitive data or areas
- Simulate social engineering attacks to evaluate employee readiness
Policies supported by training and enforcement empower employees to act as the first line of defense against social engineering.
Emerging Trends in Social Engineering
Attackers are continuously adapting social engineering methods with technological advances:
- AI-Generated Phishing: Highly convincing automated emails that are difficult to detect.
- Deepfake Vishing: Manipulated voice or video to impersonate trusted individuals.
- Hybrid Attacks: Combining social engineering with malware or ransomware for increased effectiveness.
- Exploitation of Remote Work: Targeting distributed teams through messaging apps and video conferencing platforms.
Organizations must remain adaptable and update training and detection tools regularly.
Real-World Case Studies
Case Study 1: Financial Institution Breach
A spear-phishing email impersonated senior executives, leading to unauthorized fund transfers and exposing client account details.
Case Study 2: Healthcare Data Compromise
A hospital employee clicked a phishing link posing as IT support, installing malware that accessed patient records and triggered regulatory penalties.
Case Study 3: Corporate Conference Baiting
Malicious USB drives at a technology conference infected corporate laptops with malware, causing operational disruptions and data loss.
These examples demonstrate the diverse approaches and serious consequences of social engineering attacks.
Key Takeaways
- Social engineering exploits human behavior, not technical flaws.
- Attack methods include phishing, spear phishing, pretexting, baiting, tailgating, vishing, and smishing.
- Consequences include financial loss, data breaches, legal penalties, and reputational damage.
- Prevention requires training, technical safeguards, verification processes, and cybersecurity policies.
- Emerging threats like AI-driven phishing and deepfake attacks require continuous adaptation.
Frequently Asked Questions
1. What is social engineering in cyber security?
Social engineering is a technique attackers use to manipulate people into revealing confidential information or performing actions that compromise security.
2. How can organizations protect themselves from social engineering attacks?
Through employee training, multi-factor authentication, verification protocols, email filters, and regular security audits, organizations can reduce risk.
3. Are social engineering attacks only digital?
No, attacks can also occur physically, such as tailgating or baiting, exploiting human behavior in the real world.
Disclaimer
This article is for informational purposes only and reflects cybersecurity trends and best practices in 2025. It does not constitute legal, financial, or professional advice. Organizations and individuals should consult cybersecurity experts for tailored strategies.